The Vigenère Cipher: Introduction


The Vigenère cipher first appeared in the 1585 book
Traicté des Chiffres
(A Treatise on Secret Writing)
by Blaise de Vigenère.

However, Giovan Batista Belaso discussed a similar technique in his 1553 booklet La cifra del. Sig. Giovan Batista Belaso [KAHN1967, page 137]. Singh [SINGH1999, pp. 45--51, Chapter 2] has a short and interesting discussion about Vigenère, which is quoted below, and Kahn [KAHN1967, page 137, Chapter 4] has a longer and more detailed exposition. On the other hand, the book of Vigenère did present an auto-key system, which is perhaps his major contribution to cryptography in addition to the Vigenère cipher. We will not discuss this auto-key systems.
Vigenère became acquainted with the writings of Alberti, Trithemius and Porta when, at the age of twenty-six, he was sent to Rome on a two year diplomatic mission. To start with, his interest in cryptography was purely practical and was linked to his diplomatic work. Then, at the age of thirty-nine, Vigenère decided that he had accumulated enough money for him to be able to abandon his career and concentrate on a life of study. It was only then that he examined in detail the ideas of Alberti, Trithemius, and Porta, weaving them into a coherent and powerful new cipher [SINGH1999, page 46.
......
Although Alberti, Trithemius and Porta all made vital contributions, the cipher is known as the Vigenère cipher in honour of the man who developed it into its final form. The strength of the Vigenère cipher lies in its using not one, but 26 distinct cipher alphabets to encode a message [SINGH1999, 48].
......
To unscramble the message, the intended receiver needs to know which row of the Vigenère square has been used to encipher each letter, so there must be an agreed system of switching between rows. This is achieved by using a keyword [SINGH1999, page 49].
......
Vigenère's work culminated in his A Treatise on Secret Writing, published in 1586. Ironically, this was the same year that Thomas Phelippes was breaking the cipher of Mary Queen of Scots. If only Mary's secretary had read this treatise, he would have known about the \VIG cipher, Mary's messages to Babington would have baffled Phelippes, and her life might have been spared [SINGH1999, page 51.
The next few pages focus on the basics of the Vigenère cipher. The Vigenère Cipher Encryption and Decryption explains the cipher and the encryption and decryption processes, Other Vigenère Cipher Devices discusses two devices, disk and slide, that make the encryption and decryption process easier than the use of the Vigenère table, and The Algebraic Nature of the Vigenère Cipher talks about the way of programming a Vigenère cipher. The Vigenère Cipher Encryption and Decryption cipher is simple and easy to understand and implement. However, for nearly three centuries the Vigenère cipher had not been broken until Friedrich W. Kasiski published his 1863 book. Note that Charles Babbage also used a similar technique and successfully broke the Vigenère cipher in 1846; but he did not publish his work.
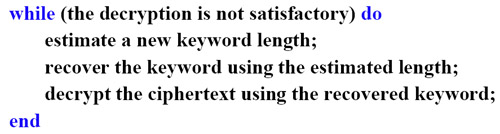
This tutorial discesses two methods for breaking the Vigenère cipher. Kasiski's Method Kasiski's method to find a possible length of the unknown keyword. The Index of Coincidence page presents the Index of Coincidence (IOC, IoC or IC) method proposed in 1922 by William F. Friedman. This method is used find the length of the unknown keyword (Keyword Length Estimation with Index of Coincidence). Once a possible length of the unknown keyword is found, the χ2 method is used to recover the keyword. Since the estimation of keyword length may not be correct, a number of iterations may be needed. Hence, to decrypt a ciphertext encrypted with the Vigenère cipher, one usually follows an iterative procedure as shown below. Finally, Complete Examples provides several complete examples.


|

|

|